Solving WooCommerce Checkout Race Conditions with Redis Redlock
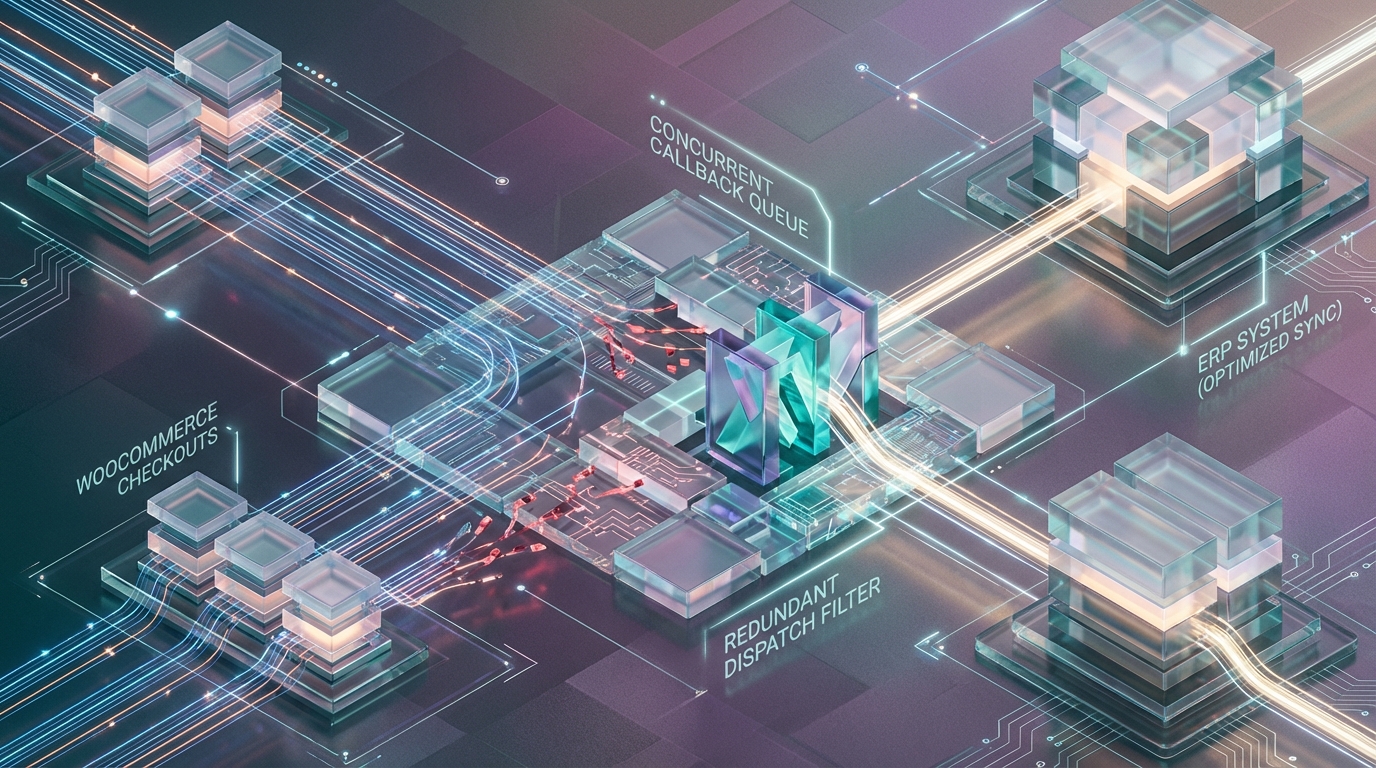
The WooCommerce payment completion flow is inherently vulnerable to a Time-of-Check to Time-of-Use (TOCTOU) race condition. At scale, the final stage of a checkout sequence splits into two distinct, concurrent network requests hitting the origin server: the asynchronous payment provider webhook (e.g., Stripe’s payment_intent.succeeded event) and the synchronous client-side redirect (the return_url).
When these requests arrive at the reverse proxy concurrently, the application routes them to separate PHP-FPM worker threads. The resulting race condition corrupts system state, leading to catastrophic downstream effects like duplicate ERP dispatch events, corrupted inventory levels, and repeated fulfillment requests.
The failure mode follows a strict, predictable sequence:
- Thread A (Webhook) and Thread B (Sync Redirect) execute
WC_Order::payment_complete()or custom status transition logic simultaneously. - Both threads read the current order status (
pending) into PHP memory. - Both threads validate the state transition and update the database order status to
processingorcompleted. - Both threads fire the critical
woocommerce_payment_completeandwoocommerce_order_status_{status}hooks. - External observers bound to these hooks (such as ERP integration plugins or inventory controllers) execute twice.
The Race Window: Within standard PHP-FPM and MySQL architectures, the typical read-modify-write cycle takes ~40-120ms. If the webhook and the synchronous redirect penetrate the application layer within this delta, the duplicate dispatch is virtually guaranteed. The default database isolation level (InnoDB’s REPEATABLE READ) entirely fails to prevent this application-level duplication. This occurs because WC_Order::save() does not inherently issue SELECT ... FOR UPDATE locks during its state evaluation phase.
The MySQL Isolation Trap and WordPress Core Limitations
Migrating to WooCommerce’s High-Performance Order Storage (HPOS) resolves substantial read-latency issues by shifting data from the heavily fragmented wp_postmeta table to dedicated wp_wc_orders tables. However, HPOS is an indexing and schema optimization; it is not a concurrency control mechanism. Standard WooCommerce CRUD operations do not enforce strict row-level locking for state transitions out of the box.
Reliance on Application-Level State
WooCommerce abstracts database interactions through the WC_Order object. When WC_Order::get_status() is invoked, the state is cached within the object instance in application memory. In a highly concurrent environment, by the time Thread A updates the database, Thread B has already hydrated its WC_Order instance with stale data.
Absent Pessimistic Locking
The core method handling the financial conclusion of a checkout, WC_Order::payment_complete(), does not wrap the state transition in a serialized transaction. It lacks pessimistic concurrency control mechanisms, failing to utilize GET_LOCK() or SELECT ... FOR UPDATE. Consequently, the storage engine permits both threads to execute their UPDATE statements sequentially, without blocking the read operations that preceded them.
Hook Synchronicity and Transaction Boundary Bloat
WordPress hooks are inherently synchronous and blocking. If an engineer attempts to wrap the transition in a manual database transaction, the synchronous execution of downstream hooks introduces severe instability. If an ERP API call takes 30 seconds to resolve within the woocommerce_payment_complete hook, the database transaction boundary is held open for the duration of that external network request. Under load, this rapidly leads to connection pool exhaustion or triggers the innodb_lock_wait_timeout (which defaults to 50s in standard MySQL configurations), causing cascading failures across the entire checkout infrastructure.
Implementing Redis-Backed Distributed Locking (Redlock)
To guarantee idempotency across distributed worker nodes without relying on long-lived database transactions, the architecture requires an external coordination layer. Implementing a Redis-backed distributed lock (utilizing the Redlock algorithm principles) intercepts the request at the earliest point of order modification.
For single-node Redis deployments, or managed instances like AWS ElastiCache, a strict SET ... NX PX implementation provides sufficient atomic guarantees to prevent the TOCTOU vulnerability.
Configuration Prerequisites
Before implementing the locking mechanism, the Redis eviction policy must be explicitly configured. Set maxmemory-policy noeviction on the lock cluster. If the cluster experiences memory pressure and evicts a lock key using an LRU or LFU algorithm, idempotency guarantees will silently fail in production, immediately resurrecting the race condition.
Furthermore, this lock must be initiated precisely at the state transition boundary. Hook into woocommerce_valid_order_statuses_for_payment_complete or equivalent pre-transition hooks to evaluate lock acquisition before any state hydration or database writes occur.
Core Logic Implementation
The following PHP implementation utilizes the phpredis extension to enforce atomic lock acquisition and release.
Architectural Placement: Custom payment transition logic or ERP dispatch listeners must be wrapped within this locking mechanism. If acquireLock returns false, the system must gracefully abort the operation in the current thread, treating it as a safe no-op. This allows the thread actively holding the lock to handle the solitary dispatch. The Lua script in releaseLock is critical: it guarantees that a thread cannot accidentally release a lock that expired and was subsequently acquired by a competing thread.
Edge Case Handling: Staleness, Timeouts, and High Availability
Distributed locking introduces new failure domains. An unoptimized lock implementation merely shifts the bottleneck from the database to the application memory.
1. Lock Staleness & Slow Third-Party APIs
The Edge Case: Thread A acquires the lock and initiates a synchronous HTTP request to the ERP system. The ERP API degrades and takes 35 seconds to respond. Because the Redis lock TTL is set to 30 seconds (LOCK_TTL_MS), the lock expires natively in Redis while Thread A is still waiting for I/O. Thread B (a webhook retry or a manual user refresh) arrives, successfully acquires the newly freed lock, and dispatches a second request to the ERP. The Solution:
Decoupling (Preferred): Never make synchronous external API calls inside the lock boundary. Utilize the locked transition exclusively to emit an event payload to a Message Broker (such as RabbitMQ or Kafka) or an asynchronous background worker queue like WooCommerce’s Action Scheduler. By decoupling the network I/O from the state transition, the lock is held only for the <50ms required to commit the local database state and push the job to the queue.
Watchdog Pattern: If synchronous calls within the execution thread are absolutely unavoidable due to legacy constraints, implement a background heartbeat thread to dynamically extend the lock TTL (PEXPIRE in Redis) while the API call is in flight.
2. Lock Acquisition Timeouts & Webhook Collisions
The Edge Case: Thread B (the Return URL sync redirect) fails to acquire the Redis lock because Thread A (the Stripe Webhook) currently holds it. The Solution: You cannot simply terminate the process without handling the client and the payment provider appropriately.
For the Webhook thread: If the webhook fails to acquire the lock, return an HTTP 409 Conflict or HTTP 429 Too Many Requests. Payment gateways natively respect these status codes and will schedule a retry utilizing exponential backoff, ensuring eventual consistency without forced duplication.
For the Sync Redirect thread: If the client redirect fails to acquire the lock, bypass the ERP dispatch logic entirely. Redirect the user immediately to the standard “Order Received” front-end route. The UI should display a generic “Processing” state. The final state confirmation should be offloaded to a subsequent client-side polling request or a WebSocket push, abstracting the lock collision from the end user.
3. Redis High Availability & Failover Degradation
The Edge Case: The Redis cluster undergoes a failover event, or a transient network partition isolates the PHP-FPM application nodes from the Redis master. The acquireLock method throws connection exceptions, halting all checkout progressions. The Solution: Implement graceful degradation to MySQL application-level locks.
If the Redis connection drops, the system must immediately fallback to GET_LOCK('wc_order_erp_disp_' . $order_id, 3). While this architecture couples locking directly to the primary database node and introduces overhead to the connection pool, it maintains strict system idempotency during severe infrastructure anomalies.
Architectural Benchmarks: Before vs. After
Implementing a distributed lock and decoupling the network I/O structurally transforms the performance profile of the WooCommerce checkout boundary. The metrics below outline the transition from default synchronous core behavior to a decoupled, Redis-backed architecture.
| Metric / Characteristic | Legacy Core Execution (Synchronous) | Redis-Backed + Decoupled Execution |
|---|---|---|
| TOCTOU Race Window | ~40-120ms (Unprotected) | 0ms (Guaranteed via SET NX) |
| Lock Holding Window | N/A (No locks held) | <50ms |
| Max Transaction Boundary | Up to 50s (Hitting innodb_lock_wait_timeout) |
Dependent only on local MySQL I/O |
| ERP API Latency Impact | 35s+ blocks worker thread & DB | 0ms impact on origin worker thread |
| Idempotency Guarantee | None (Fails on concurrency) | Absolute (Bounded by Redis cluster availability) |
| Infrastructure Degradation | Cascading DB connection pool exhaustion | Graceful fallback to GET_LOCK() |
By shifting the architectural boundary, the origin server is completely shielded from external ERP latency, and the database connection pool remains highly available even during severe webhook concurrency spikes.
Azguards Technolabs: Performance Audit and Specialized Engineering
Engineering robust, idempotent payment flows in high-volume e-commerce environments requires more than basic plugin configuration; it demands architectural precision. At Azguards Technolabs, we specialize in Performance Audit and Specialized Engineering for enterprise infrastructure.
When standard WooCommerce architectures reach their concurrency limits, our engineering teams dismantle the bottlenecks. Whether it involves transitioning monolithic synchronous hooks into distributed Kafka event streams, mitigating TOCTOU vulnerabilities, or restructuring database isolation strategies for HPOS, Azguards provides the technical rigor required to stabilize and scale enterprise systems. We do not just patch issues; we architect resilience.
The concurrent execution of payment webhooks and client redirects in WooCommerce is a fundamental architectural reality. Relying on default PHP memory states and standard InnoDB REPEATABLE READ isolation virtually guarantees duplicate event dispatches and corrupted ERP data under load.
Resolving this requires moving the concurrency control out of the relational database and into a distributed coordination layer. By implementing the Redlock algorithm via Redis SET NX PX, deploying atomic Lua scripts for release evaluation, and entirely decoupling the synchronous third-party network requests into Message Brokers, engineering teams can close the ~40-120ms race window entirely.
If your backend infrastructure is experiencing untraceable duplicate orders, database lock timeouts, or connection pool exhaustion during peak traffic events, standard optimizations will not suffice. Contact Azguards Technolabs for a comprehensive architectural review and complex system implementation.
Would you like to share this article?
Build Architecturally Resilient E-Commerce
Stop duplicate orders and race conditions from crippling your scale. Get a comprehensive architectural audit from our expert engineering team.
Expert engineering for high-volume enterprise systems.
All Categories
Latest Post
- Solving WooCommerce Checkout Race Conditions with Redis Redlock
- Eliminate the LLM Padding Tax: Optimizing Triton & TRT-LLM
- The TOAST Bloat: Mitigating Postgres Write Degradation in High-Volume N8N Execution Logging
- HPOS Migration Under Fire: Eliminating WooCommerce Dual-Write IOPS Bottlenecks at Scale
- The Alignment Cliff: Why Massive Python Time-Series Joins Trigger OOMs — and How to Fix Them