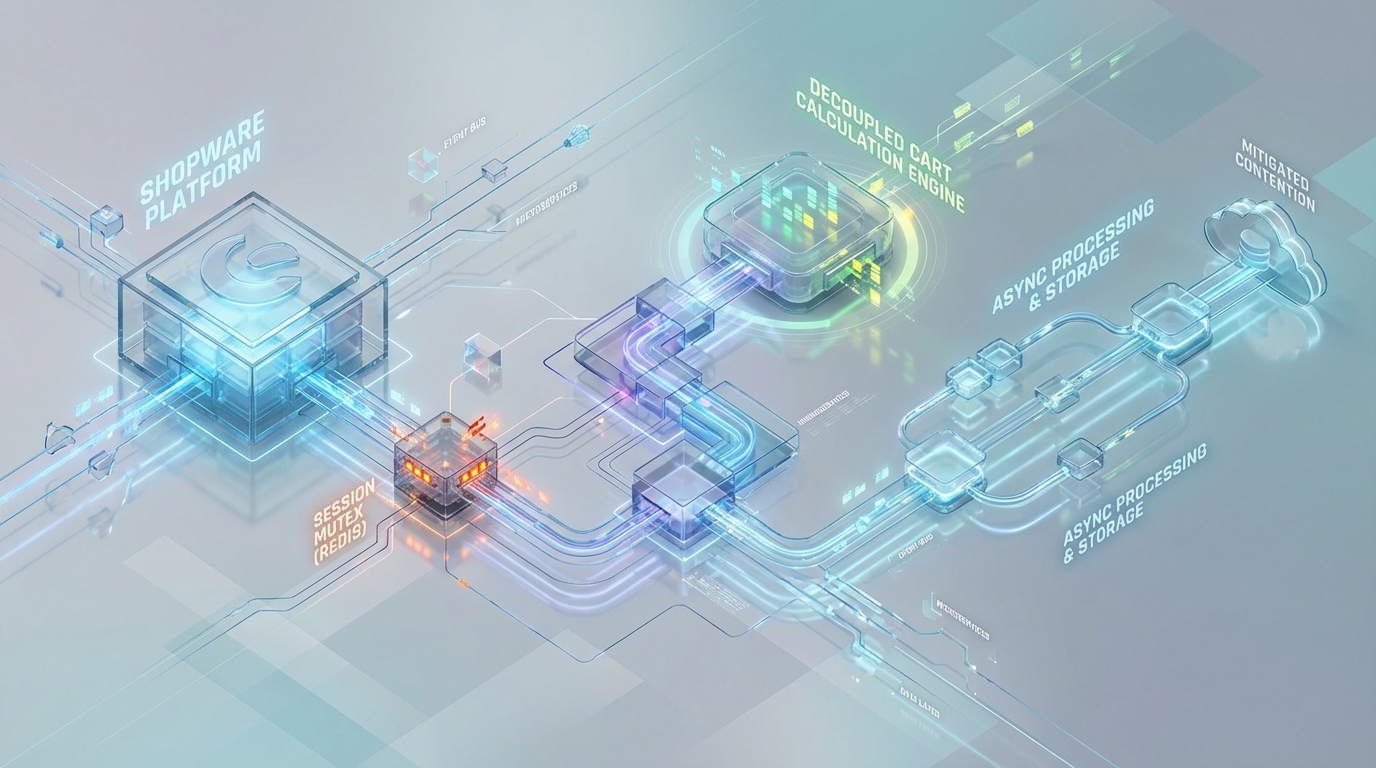
Mitigating Redis Lock Contention: Decoupling Shopware Cart Calculations from Session Mutexes
The Situation, Complication, and Resolution
Architecting high-concurrency state management in e-commerce requires strict boundaries between ephemeral synchronization and heavy business logic execution. For engineering teams running enterprise Shopware 6 infrastructure, flash sales, high-velocity bot traffic, or even aggressive headless Single Page Application (SPA) polling frequently expose a severe architectural bottleneck: session mutex contention.
The Situation: Shopware 6 utilizes Symfony’s underlying HTTP Foundation for request handling and session management. In distributed deployments, session state is typically persisted in Redis using the RedisSessionHandler via the native phpredis extension.
The Complication: By default, Symfony and phpredis enforce strict synchronous session locking. When high-concurrency cart mutations trigger the Shopware CartRuleLoader, the thread acquires an exclusive Redis spinlock (SETNX). Because the Data Abstraction Layer (DAL) processing is heavily CPU and I/O bound, parallel requests from the same user session queue up, rapidly exhausting PHP-FPM worker pools and resulting in cascading 502 Bad Gateway and 504 Gateway Timeout errors.
The Resolution: Stabilizing Shopware for extreme transaction volumes requires fundamentally uncoupling the cart state calculation from the session mutex. This is achieved by migrating from pessimistic extension-level locking to optimistic application-level concurrency control, entirely bypassing session constraints via headless headers, or implementing asynchronous validation queues.
Execution Trace: The Flash Sale Mutex Contention
To dismantle the bottleneck, we must first trace the precise execution path of a concurrent cart mutation. The contention does not occur at the database layer; it manifests at the L7/FPM interface before the application can even dispatch its core logic.
The Execution Path
- L7 Ingress: A client application fires multiple concurrent XHR/API requests sharing the same session identifier. For example, a frontend application simultaneously triggers
POST /store-api/checkout/cart/line-itemandGET /store-api/context. - PHP-FPM Bootstrap: The ingress controller (e.g., Nginx) proxies the request payload to the PHP-FPM process manager. Symfony boots up, initializes the HTTP kernel, and processes the request headers.
- Session Intercept: Before business logic executes, Symfony triggers the configured
RedisSessionHandlerto hydrate the user state. - The Lock (The Bottleneck): When
redis.session.locking_enabled=1is configured natively, thephpredisextension executes a RedisSETNX(Set if Not eXists) command to acquire an exclusive spinlock for thePHPSESSID. - Context Generation & Cart Calculation: The single FPM thread holding the lock proceeds to load the
SalesChannelContext. Shopware invokes theCartRuleLoader. This triggers deep traversal of the DAL to calculate aggregate taxes, evaluate active promotions via the Rule Builder, and verify inventory constraints. - Contention: While Thread A is blocked on MySQL I/O and CPU-bound Rule Builder graph execution, Threads B, C, and D (spawned by the parallel requests from the same client) enter a spinlock state in Redis. They consume FPM resources while infinitely polling for the mutex to release.
Hard Limits & Configuration Thresholds
The strict physical limits of this operation are defined by phpredis directives: redis.session.lock_retries (defaulting to 10) and redis.session.lock_wait_time (defaulting to 20000 microseconds).
If Thread A’s DAL calculation takes 500ms, Threads B, C, and D will exhaust their retry allowance after 200ms. The extension will abruptly sever the execution, throwing a fatal Session lock could not be acquired exception.
In an attempt to mask these exceptions, infrastructure teams frequently implement a reckless anti-pattern: artificially inflating lock_retries to 100 or higher. While this suppresses the immediate exception, it forces FPM threads to hang indefinitely, directly catalyzing catastrophic infrastructure failure.
Architectural Root Cause Analysis: DAL Calculations vs. FPM Exhaustion
The structural mismatch driving this outage lies in marrying a highly optimized, fast synchronization mechanism (the Redis session mutex) with slow, synchronous, complex business logic execution (the Shopware DAL).
The “Death Spiral” Mechanics
Because the CartRuleLoader processes the cart payload synchronously within the active session lifecycle, response times degrade rapidly as cart complexity increases. A payload with 15+ line items mapped against complex nested rules (e.g., evaluating “10% off if Category X and Customer Group Y” across multiple dimensions) routinely pushes API response times into the 400ms – 800ms range.
When a frontend client initiates parallel requests sharing the same Session ID:
- One request successfully acquires the Redis lock and executes the
CartRuleLoaderfor 800ms. - The remaining parallel requests occupy distinct PHP-FPM workers, completely idling in a Redis spinlock waiting for the initial request to finalize.
- OOM / Pool Exhaustion Threshold: Consider a standard application node equipped with 16GB RAM and 8 vCPUs, configured with an FPM pool of
pm.max_children = 150(assuming roughly 100MB per process). It requires merely ~20 users triggering 8 concurrent locked requests (e.g., aggressive SPA behavior during a hype drop) to entirely starve the worker pool. - Cascading Failure: Once the
max_childrenthreshold is breached, the Nginxlistenbacklog queue fills immediately. New connections are dropped, triggering widespread 502 and 504 errors for all active users across the platform, irrespective of whether they are experiencing session contention.
Production-Grade Mitigations
To stabilize Shopware 6 for enterprise-grade transaction volumes, engineering teams must entirely uncouple cart state mutations from the native session mutex. The following three architectural mitigations represent production-validated pathways to resolving FPM starvation.
Mitigation A: Overriding RedisSessionHandler for Lock-Free Optimistic Reads
Pessimistic native locking operates at the C-extension level, remaining entirely ignorant of application context or business intent. To free up FPM capacity, you must disable this low-level lock and implement a custom Symfony Session Handler reliant on Optimistic Concurrency Control (OCC).
Infrastructure Configuration: First, disable native phpredis locking within your framework.yaml configuration or directly via the php.ini DSN:
Architectural Pattern: With extension-level locking disabled, implement a custom session handler satisfying the SessionUpdateTimestampHandlerInterface.
Reads: Perform a strictly lock-free GET operation against Redis. Multiple FPM threads can now hydrate the session concurrently without blocking.
Writes: Maintain an in-memory hash of the session payload upon instantiation. Before writing back to Redis during the kernel termination phase, evaluate if the payload has actually mutated. If a write is necessary, acquire an application-level Symfony Lock via an atomic Redis Lua script (EVAL) for the microsecond duration of the write.
Collision Handling: If a collision occurs on write, enforce a “last-write-wins” policy or discard non-critical session data. Because the highly critical Cart payload is stored structurally separate in Shopware 6, volatile session overrides carry minimal risk to transactional integrity.
Mitigation B: Bypassing Sessions via Headless sw-context-token
Shopware 6’s core architecture cleanly delineates the cart payload—managed via the Cart Persister from the session identifier. For teams leveraging headless architectures (such as Vue Storefront or Next.js), completely eliminating PHP session cookies represents the most resilient path forward.
By removing the session cookie, you strip Symfony of the trigger that initializes the RedisSessionHandler, neutralizing the contention vector entirely.
- Token Authentication: Authenticate the client and obtain the unique
sw-context-token. - Stateless Injection: Pass the
sw-context-tokenstrictly as an HTTP Header on all subsequent Store API calls, completely omitting standard cookie headers. - The Trade-Off: The Store API is inherently stateless when utilizing header tokens. Because the
PHPSESSIDis absent, FPM workers execute immediately without checking Redis for a mutex. - Cart Persister Separation: To prevent massive cart payload data from crowding out standard application cache, isolate your cart data to a dedicated, high-I/O Redis instance. This prevents LRU (Least Recently Used) cache evictions from quietly destroying active user carts.
Mitigation C: Asynchronous Cart Validation Queues (Theoretical Engineering Model)
By default, the Shopware CheckoutOrderPlacedEvent and LineItemWritten events enforce strict synchronous recalculation. For high-velocity flash sales (e.g., limited-edition sneaker drops or high-demand ticket releases), synchronous DAL validation is a catastrophic anti-pattern. Transforming this into an asynchronous flow eliminates FPM blocking entirely.
Implementation Strategy:
- Edge-Level Intercept: Intercept the high-latency mutation route (e.g.,
POST /store-api/checkout/cart/line-item) using a lightweight Symfony Controller or an API Gateway proxy. - Intent Queuing: Extract the essential mutation parameters (Context Token, Product ID, Quantity) and push this “Add to Cart Intent” into a high-throughput message broker like RabbitMQ or a Redis Stream.
- Optimistic UI Response: Immediately return an
HTTP 202 Acceptedto the client. This releases the PHP-FPM worker back to the pool in < 15ms, entirely bypassing theCartRuleLoaderduring the HTTP request cycle. - Background DAL Calculation: Provision a dedicated pool of resilient CLI workers running
bin/console messenger:consume. These workers pull the intent from the broker, execute the synchronous, heavyCartRuleLoaderin the background, and update the isolated Redis Cart Persister. - State Synchronization: The frontend SPA maintains a connection to the infrastructure via Server-Sent Events (SSE) utilizing Mercure, or via intelligent long-polling. Once the background worker completes the reconciliation, it pushes the updated cart state to the client.
Engineering Note: This architectural shift sacrifices immediate consistency for eventual consistency. However, it ensures your backend infrastructure can absorb a 10,000 req/sec flash-sale spike without requiring an impossible FPM pool size of 10,000 workers.
Azguards Technolabs: Performance Audit and Specialized Engineering
Handling high-concurrency state management requires moving beyond standard framework defaults. When standard configurations fail under the weight of enterprise transaction volumes, generic scaling—simply adding more nodes or inflating FPM limits—only accelerates cascading failures.
At Azguards Technolabs, our focus is on resolving the hard parts of infrastructure engineering. We provide Performance Audits and Specialized Engineering for enterprise teams operating high-stakes Shopware infrastructure. Whether it involves rewriting critical paths for lock-free state management, separating persistence layers, or implementing asynchronous event-driven architectures, we architect systems designed for mathematical certainty under peak load. We integrate directly with your engineering teams to audit execution traces, dismantle architectural bottlenecks, and deploy resilient, high-throughput solutions.
Conclusion
The reliance on pessimistic Redis session locking (SETNX) fundamentally cripples Shopware 6 applications under high-concurrency conditions. By forcing heavy, synchronous CartRuleLoader operations to execute while holding a session mutex, the infrastructure creates an artificial bottleneck that quickly starves PHP-FPM worker pools.
Engineering high-availability commerce platforms dictates that state mutation and state synchronization must be decoupled. By transitioning to lock-free optimistic reads, leveraging headless sw-context-token headers to bypass the HTTP Foundation entirely, or adopting asynchronous validation queues, organizations can transition from fragile, synchronous architectures to resilient, decoupled systems capable of absorbing massive traffic spikes.
If your platform is experiencing unpredictable latency, FPM pool exhaustion, or 502/504 errors during peak transaction windows, standard auto-scaling will not resolve the underlying architectural flaw. Contact Azguards Technolabs for an expert architectural review or to assist with complex infrastructure implementations.
Would you like to share this article?
Running Shopware at Enterprise Scale?
Default framework configurations rarely survive flash-sale traffic or high-concurrency environments. If you're experiencing Redis lock contention, slow cart calculations, or PHP-FPM exhaustion, it may be time to rethink the architecture.
Talk to Our Engineering TeamAll Categories
Latest Post
- DuckDB Spill Cascades: Mitigating I/O Thrashing in Out-of-Core SEO Data Pipelines
- Beyond the TIME_WAIT Cliff: Scaling N8N Egress Velocity with Envoy Sidecar
- Mastering Distributed Rate Limiting: Eliminating the 429 Thundering Herd in Shopify K8s Topologies
- The LangChain Dynamic Schema Leak: Fixing Pydantic V2 Native Memory Exhaustion
- How Graph Reordering Eliminates L1 Cache Misses in SciPy PageRank at Scale